Not long ago, I wrote that around €5 billion in damages were caused by transferring far too much information to a lab (which also had poor security). Meanwhile, the number of victims has already risen to almost 1 million!
How do I arrive at such a high number?
Below is an overview of the costs if your private information is stolen. Why are these costs so high? Many organizations think that your date of birth, address, and citizen service number (BSN) are all less-known details that they can use to quickly determine if they are indeed talking to you on the phone. Now, relying on that is a significant risk factor.
Ten thousand euros x 1 million people results in a cost of €10 BILLION to the victims. Will anyone be able to pay that out? I’m afraid not.
What you can do is limit the impact of this theft.
If your password is stolen, you will be instructed to change it. The BSN system is not designed to allow you to obtain a new BSN. You can’t simply change your date of birth and address either. So if invalidating the data itself doesn’t work, what can be done?
What is needed is a method that can be quickly implemented to verify someone’s identity. All organizations that currently accept loans (including online stores, banks, etc.) can use this. They don’t have to, but if, despite this method, they don’t check whether it actually is you on the phone, then it’s their risk, not yours anymore…
Consider the use of DigiD; practically everyone already has it, so it can be implemented quickly. However, DigiD is only permitted for (semi-)government organizations; there are alternatives such as iDIN for commercial parties. There are certainly better methods, but they still need to be developed, and we’re in a hurry.
This means a lot of work for all the organizations that will suddenly have to integrate DigiD and iDIN, upgrades for these providers themselves, and so on.
For the companies that will have to use this, integrating such verification could cost a hundred thousand euros. The cost could be lower if you have competent people, and higher if not. These costs will therefore affect roughly 100-500 companies in the Netherlands. The direct costs of such an operation could easily reach 50 million. That is serious money, but at the same time, it’s only 1/200th of 10 billion! It’s therefore a pittance for the lab or ministry that will be held accountable for the damages suffered as a result of this leak.
What I haven’t addressed yet is how phishing based on this data will be stopped…
However, what is needed first is for the public to realize the damage stolen data can cause. That a “security risk” can and will eventually materialize. That if something goes wrong, it could mean the end of your company and potentially become a personalliability for the director who ignored the problem. Politicians also need to understand this and take it seriously.
If you’re looking for someone to lead a knowledge session at your company about this kind of issue, at the management level, please fill out the contact form!
Not long ago, I wrote that around €5 billion in damages were caused by transferring far too much information to a lab (which also had poor security). Meanwhile, the number of victims has already risen to almost 1 million!
How do I arrive at such a high number?
Below is an overview of the costs if your private information is stolen. Why are these costs so high? Many organizations think that your date of birth, address, and citizen service number (BSN) are all less-known details that they can use to quickly determine if they are indeed talking to y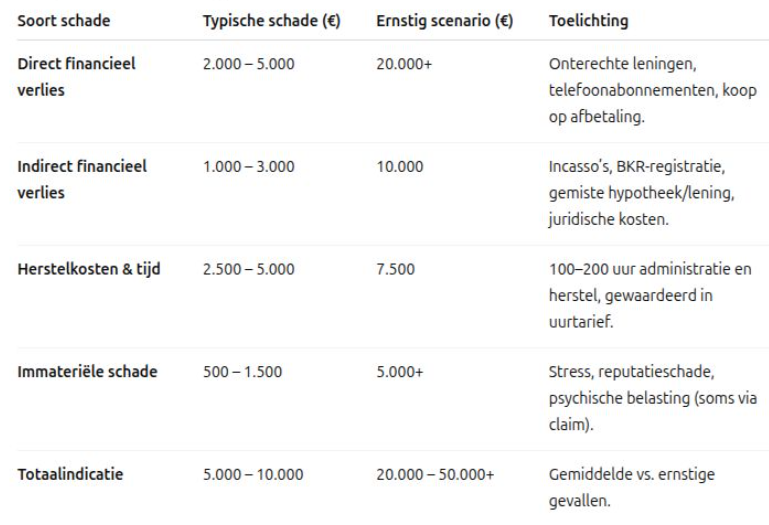 ou on the phone. Now, relying on that is a significant risk factor.
ou on the phone. Now, relying on that is a significant risk factor.
Ten thousand euros x 1 million people results in a cost of €10 BILLION to the victims. Will anyone be able to pay that out? I’m afraid not.
What you can do is limit the impact of this theft.
If your password is stolen, you will be instructed to change it. The BSN system is not designed to allow you to obtain a new BSN. You can’t simply change your date of birth and address either. So if invalidating the data itself doesn’t work, what can be done?
What is needed is a method that can be quickly implemented to verify someone’s identity. All organizations that currently accept loans (including online stores, banks, etc.) can use this. They don’t have to, but if, despite this method, they don’t check whether it actually is you on the phone, then it’s their risk, not yours anymore…
Consider the use of DigiD; practically everyone already has it, so it can be implemented quickly. However, DigiD is only permitted for (semi-)government organizations; there are alternatives such as iDIN for commercial parties. There are certainly better methods, but they still need to be developed, and we’re in a hurry.
This means a lot of work for all the organizations that will suddenly have to integrate DigiD and iDIN, upgrades for these providers themselves, and so on.
For the companies that will have to use this, integrating such verification could cost a hundred thousand euros. The cost could be lower if you have competent people, and higher if not. These costs will therefore affect roughly 100-500 companies in the Netherlands.
The direct costs of such an operation could easily reach 50 million. That is serious money, but at the same time, it’s only 1/200th of 10 billion! It’s therefore a pittance for the lab or ministry that will be held accountable for the damages suffered as a result of this leak.
What I haven’t addressed yet is how phishing based on this data will be stopped…
However, what is needed first is for the public to realize the damage stolen data can cause. That a “security risk” can and will eventually materialize. That if something goes wrong, it could mean the end of your company and potentially become a personal liability for the director who ignored the problem. Politicians also need to understand this and take it seriously.
If you’re looking for someone to lead a knowledge session at your company about this kind of issue, at the management level, please fill out the contact form!